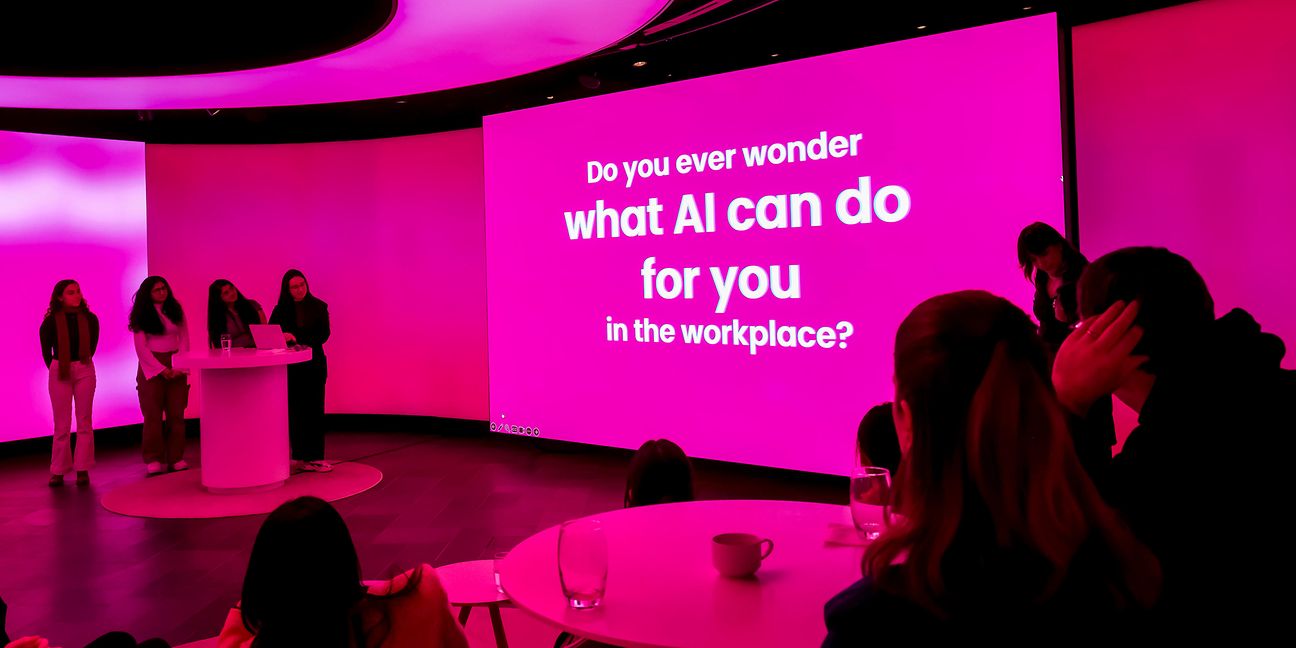
Getting to know each other: Femtec scholarship holders at Deutsche Telekom
The female STEM students learn about Deutsche Telekom's initiatives “Against Hate on the Net” and against phishing, gather information in the World Café and tour the Cyber Defense Center.
9 weeks